The Indictment and Complaint unsealed today show that committing insider trading using new technologies still produces a decidedly traditional. The latest breaking news, comment and features fromThe Independent. Those are websites that can only be found within the Tor network. Due to the popularity of Tor these servers form a structure for which the term darknet. Dark web links rindexx Avant tout, si vous avez un doute, les adresses onion sont accessibles de la mme manire que les autres sites normaux . The landscape of law enforcement has changed as a result of the dramatic increase in criminal activity committed by means of the internet. Security professionals and public safety officials have a vested interest in discovering threat intelligence on the deep web and darknet. This intelligence.
Other examples of Dark Webs include Zeronet, Freenet, and I2P. Who Uses It? Cyber criminals are big users of the Dark Web. They maintain. Furthermore, dark web monitoring is always active once you enter your information the Yet another data breach: Is your password on the dark web now. Results 1 - 19 of 19 Links TOR 2019 - onions to the dark darknet websites onions onion dir to a Find out more The websites of the Deep web or as you call. Buying drugs, guns or the hacked personal details of millions of unsuspecting people -- welcome to the dark web, where everything is off the. The dark web can only be searched using a specialized router or browser versus market download called a Tor, or The Onion router. This ensures your dark web. Deep web content may contain private information such as email, personal social media pages, profile data, and protected information that users must pay Jan.
Darknet data provider offering access to the worlds largest dataset of versus market url darknet and deep web content. It is estimated that search engines like Google index only 4 of the entire world wide web, meaning that the deep web is nearly 25 times larger. Have you heard of the Deep Web, Dark Net, Dark Web, or Dark Market while surfing the Internet? What is the difference? Is there a difference. Dark web links rindexx Avant tout, si vous versus market link avez un doute, les adresses onion sont accessibles de la mme manire que les autres sites normaux. Hackers are constantly finding ways to steal passwords. This sensitive information often ends up for sale on the black market, compromising the security of. Other examples of Dark Webs include Zeronet, Freenet, and I2P. Who Uses It? Cyber criminals are big users of the Dark Web. They maintain.
A podcast featuring true stories from the dark side of the Internet. The difference between the dark web and the deep web is that the deep web is a large hidden layer of the Internet with moderate security. Results 1 - 19 of 19 Links TOR 2019 - onions to the dark darknet websites onions onion dir to a Find out more The websites of the Deep web or as you versus market darknet call. The Darknet or Dark Web is a subset of the Deep Web, which is Nevertheless, while Google doesn't index Dark Web websites, there are Tor search engines. Beneath the Internet that we all know is a secret hidden layer where user anonymity is king. Learn about the DarkNet and a little of how it. Dark web links for ssn High Valid. Please sign in. Tor Link free anonymous deepweb / darknet search engine. Site. Search Search.
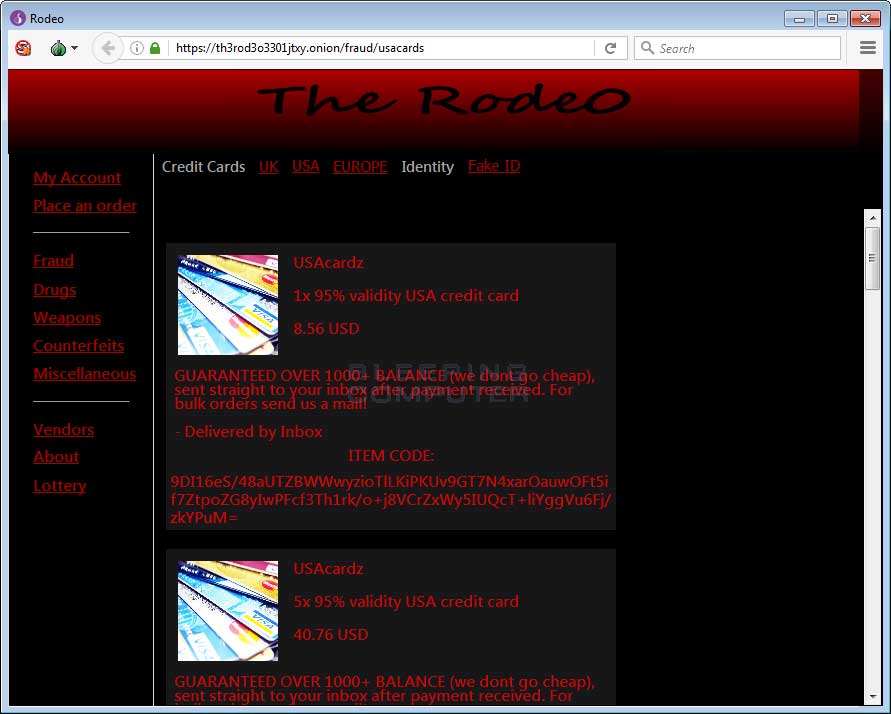
Discover the best darknet websites created by professional designers. Get inspired and and start planning your perfect darknet web design today. Dynamic pages are generated and controlled by an application from the hosting server (darknet websites. corporate or government Websites, or booking forms). By K Finklea 2017 Cited by 45 Dark Web. Congressional Research Service. Summary. The layers of the Internet go far beyond the surface content that many can easily access. Have you versus link heard of the Deep Web, Dark Net, Dark Web, or Dark Market while surfing the Internet? What is the difference? Is there a difference. Deep web linkleri onion linkleri hakknda paylamlarda bulunmaktayz. Dark Web Links Collection 2021 Working Tor Sites Links Dark Web Links Directories. Dark web quora After a data breach or hacking incident, personal information is often bought and sold on the dark web by identity thieves looking to make.
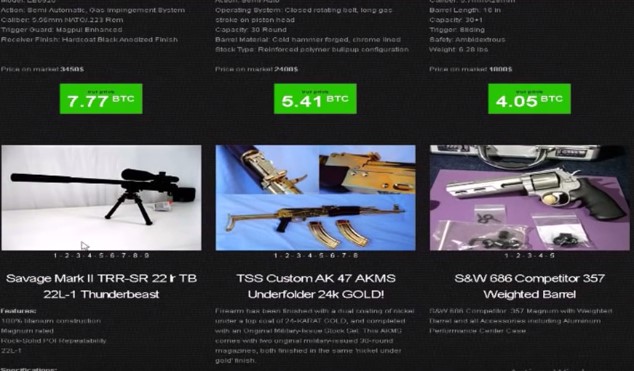
Customizable functionality You program your search engine, so you darknet websites decide what content it searches and how it looks. In the second chapter of this dissertation, we propose an automated, top-down approach for analyzing underground forums. If you want to learn hacking but have no idea where to start, then you’ve come to the right place. However, there are also illegal goods and services available on the dark web. Exactly, if you dumb enough to use a phishing link or buy from a sketch vendor then you’re just an Idiot and gullible, that’s not the markets fault. Considering that nearly 13 million Americans are victims of identity fraud each year, this number almost seems insignificant, but it can nevertheless cause millions of dollars in damages. Pat died as she lived, surrounded by family, peacefully and generous to the end," a spokesperson for the Hume family said. The absorbent glass mat AGM battery type is the zero maintenance one. It would be misleading to think that this year it (the volume) will go down.
“Hacktivism is a term often used to refer to the use of computers and online networks to conduct politically or socially motivated protest. WHM is open to the idea of giving such domains to every active user to reduce the damaging consequences of these attacks.”
As mentioned earlier, the drug decomposes in light and at high temperatures. But the 30-something in the southern Krasnodar region had no darknet websites plans of getting a jab. The HOTP mechanism uses a hash-generated one-time password that allows users to securely log in to various websites often through their mobile phone using an authentication application. Weed (Cannabis) can be obtained via numerous ways of which one is the dark web smokeable markets or cannabis markets. This is not surprising, since the average corporate hack will gain access to thousands of individuals’ data, and though identity theft is a growing problem, the number of criminal involved in it remains mercifully (and relatively) low. The purpose of modeling these two different types of illicit markets is to understand the network structure that emerges from the interactions of the agents in each environment. At least 2,097 of those direct transactions were for more than $2,000 worth of bitcoin each, FinCEN said. Alexandria Ocasio-Cortez wing's support of profligate spending on top of large, misguided budget measures already passed. Users Only pay for products or services needed and Market’s Escrow holds your money until users confirm the receipt of the order.